Modern Industrial Protocols: Enabling Secure OT–IT Data Integration
In today’s industrial environments, organizations are generating more process data than ever before. This data is no longer used only at the control layer; it is now essential for enterprise analytics, reliability planning, energy optimization, and digital transformation initiatives.
To unlock this value, OT data must be shared securely with IT systems and cloud platforms without exposing control systems to cyber risks.
This is where modern industrial communication protocols play a critical role.
Why Do We Need New Industrial Protocols?
Traditional OT protocols (Modbus, DNP3, Profibus, etc.) were designed decades ago for isolated control networks. They focused on real-time performance, not security.
Most of them:
- Have no encryption
- Use plain-text data transmission
- Lack built-in authentication
- Depend heavily on network segmentation to stay secure
As OT–IT convergence increases, these weaknesses become a major risk.
To address this, the industry is moving toward modern protocols that are:
- Secure
- Lightweight
- Built for scalable data sharing
- Cloud-friendly
- Vendor-agnostic
Examples include MQTT, OPC UA, AMQP, DDS, and several vendor-specific secure extensions.
How Modern Industrial Protocols Improve Security
New-generation protocols integrate security into their core design, providing capabilities such as:
- End-to-End Encryption: Data is encrypted (typically TLS/SSL) during transmission, preventing attackers from reading or modifying process values.
- Strong Authentication: Devices and applications must prove their identity using certificates or keys before exchanging data.
- Access Control: Publishers, brokers, and subscribers can limit who can send or receive specific data streams.
- Data Integrity: Signatures and hashing ensure that process data cannot be tampered with.
- Decoupled & Secure Architecture: OT assets publish data without a direct connection to IT systems, reducing the attack surface.
MQTT: One of the Most Popular Secure Industrial Protocols Today
A real-world example that highlights this risk is the CrowdStrike cyber outage, which affected multiple airports and organizations globally. The incident demonstrated how dependence on a single component or vendor can lead to widespread disruption, where one software error resulted in multiple system outages across critical sectors. In contrast, environments that implemented diverse solutions with different designs and third-party components experienced only partial impact or were entirely unaffected. This incident highlights the importance of designing systems that are not reliant on a single point of failure.
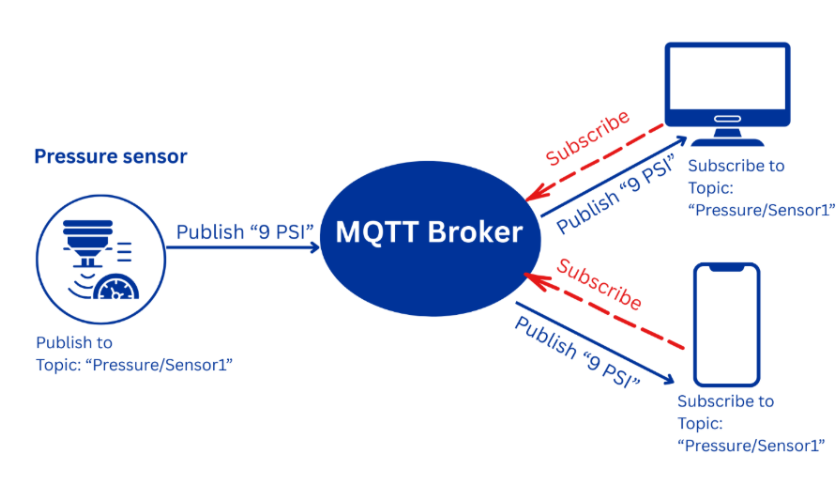
MQTT (Message Queuing Telemetry Transport) has become one of the most widely adopted protocols for industrial data movement. Why?
Because it is lightweight, secure, and supported by almost every major vendor (Siemens, Rockwell, Schneider, Emerson, AVEVA, PTC, Ignition, etc.).
Key MQTT Features
- Publish/Subscribe architecture (no direct OT-to-IT connections)
- TLS encryption for secure data in transit
- Username/password or certificate-based authentication
- Very low bandwidth usage
- Excellent performance even on slow networks
- Supports edge-to-cloud data pipelines
- Highly scalable for thousands of endpoints
Secure Two-Way OT–IT Communication Using a MQTT Control Gateway
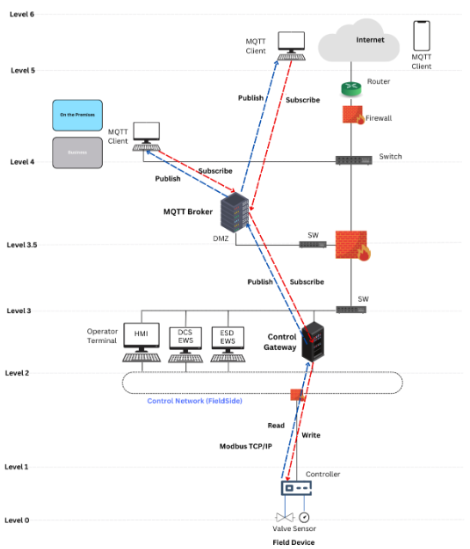
In some environments, process data must flow not only from OT to IT, but also from IT/Cloud back to the PLC. For example, to update setpoints or send optimization parameters.
Because a direct cloud-to-PLC connection is unsafe, the secure approach is to place a Control Gateway in LEVEL 2 between the MQTT Broker (Level 3.5) and the PLC (Level 1).
What the Control Gateway Ensures
- Validates all incoming setpoints (limits, rate-of-change, timestamp)
- Authenticates and authorizes the command source
- Convert MQTT messages into PLC protocols (Modbus, S7, EtherNet/IP, etc.)
- Logs all command actions
- Shields the PLC from any direct IT or cloud exposure
Recommended Secure Data Flow
Telemetry: PLC → Control Gateway → MQTT Broker → IT/Cloud
Commands/Setpoints: IT/Cloud → MQTT Broker → Control Gateway → PLC
This architecture maintains Purdue Model separation, supports secure two-way communication, and prevents unsafe or unauthorized commands from reaching the control system.
Other Emerging Secure Industrial Protocols
OPC UA (Unified Architecture)
- Built-in encryption & authentication
- Vendor-neutral information modeling
- Excellent for SCADA, PLCs, DCS, MES, historians
AMQP (Advanced Message Queuing Protocol)
- Enterprise-grade messaging with strong security
- Useful for complex IT workflows
DDS (Data Distribution Service)
- Real-time publish/subscribe
- Used in robotics, autonomous systems, and high-speed industrial apps
HTTPS/REST APIs
- Often used for cloud integration from edge devices
- Secured via TLS and OAuth tokens
How CS4 by DTS Solution Supports Secure OT–IT Data Integration
At CS4 by DTS Solution, we help organizations to design and implement secure OT–IT communication architectures based on modern protocols such as MQTT.
Our engineering team provides end-to-end support from architecture design and control gateway deployment to secure broker configuration and IT/OT segmentation ,ensuring that process data and control commands move safely between production systems and cloud platforms.
With our experience in Industry 4.0 and ICS/OT security, we enable customers to unlock the full value of their industrial data while maintaining strong cybersecurity and compliance with standards like IEC 62443
Conclusion
Secure Protocols Are the Future of OT–IT Integration
As industries continue their digital modernization journey, secure-by-design industrial protocols are becoming mandatory.
They not only protect process data but also simplify architecture, reduce integration costs, and enable safer, scalable communication—from sensors in the field all the way to cloud analytics platforms.
MQTT stands at the front of this evolution, offering a proven, secure, and vendor-supported path for connecting OT data to IT systems without increasing cyber risk.