Securing AI Integration in OT/ICS Using ISA/IEC 62443: A Risk-Driven Approach for Safe and Reliable Digital Transformation
Artificial Intelligence (AI) is increasingly being introduced into Operational Technology (OT) and Industrial Control Systems (ICS) to enhance production efficiency, optimize energy consumption, and improve asset performance. These benefits are often translated directly into financial gains and operational excellence.
However, AI integration also introduces new cyber risks, particularly when AI platforms rely on internet connectivity, cloud services, or enterprise IT integration. In high-risk OT environments, unmanaged connectivity and uncontrolled data flows can lead to severe consequences impacting safety, availability, and business continuity.
ISA/IEC 62443 provides a structured and practical framework to manage these risks and enable secure AI adoption in OT/ICS.
Why AI in OT Requires a Different Security Mindset
-
Unlike traditional IT systems, OT/ICS environments:
- Control physical processes
- Operate with real-time constraints
- Prioritize availability and safety over confidentiality
When AI systems interact with OT, they are often:
- Consume large volumes of process data
- Generate optimized setpoints or control recommendations
- Interface across IT, OT, and cloud boundaries
This makes AI
Unlike traditional IT systems, OT/ICS environments:
- Control physical processes
- Operate with real-time constraints
- Prioritize availability and safety over confidentiality
When AI systems interact with OT, they are often:
- Consume large volumes of process data
- Generate optimized setpoints or control recommendations
- Interface across IT, OT, and cloud boundaries
This makes AI not just an application, but a cross-domain cyber-physical risk that must be engineered carefully.
Using ISA/IEC 62443 to Secure AI Integration
ISA/IEC 62443 is structured across multiple layers:
- General concepts and terminology
- Policies and procedures
- System-level security requirements
- Component-level security requirements
This layered structure makes it well-suited to address AI integration holistically.
-
Risk Management as the Starting Point
AI integration should begin with risk assessment, not technology selection.
Key questions include:
- What OT assets will exchange data with AI?
- What happens if AI sends incorrect or malicious setpoints?
- What is the impact on safety, production, and availability?
From this point, cybersecurity controls can be designed to reduce risk to an acceptable level, rather than blocking innovation.
-
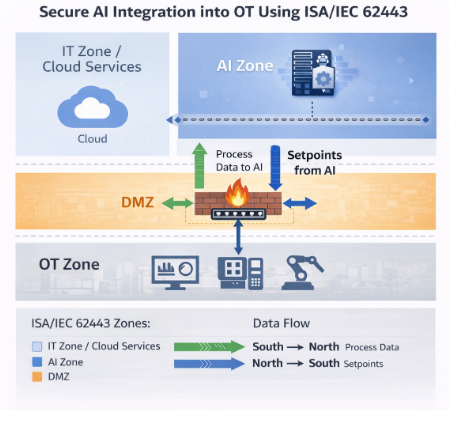
Zones and Conduits – The Core Architectural Control
Applying zones and conduits is critical when introducing AI into OT/ICS.
Recommended approach:
- Place AI platforms in a dedicated zone (typically IT, DMZ, or cloud-connected zone)
- Strictly control and monitor all conduits between AI and ICS zones
Typical data flows:
- South → North: Process data flowing from ICS to AI for analytics and optimization
- North → South: Optimized setpoints or recommendations flowing back to ICS
These conduits must be:
- Explicitly defined
- Technically enforced
- Continuously
not just an application, but a cross-domain cyber-physical risk that must be engineered carefully.
-
- Applying Foundational Requirements (FRs)
Several ISA/IEC 62443 Foundational Requirements are especially critical for AI integration:
FR#1 – Identification and Authentication: Ensure only authorized users, services, and AI components can access OT systems.
FR#2 – Use Control: Restrict what AI systems are allowed to do (e.g., advisory vs closed-loop control).
FR#3 – System Integrity: Protect against unauthorized modification of AI models, data, and setpoints.
FR#5 – Restricted Data Flow: Ensure AI communicates only through approved conduits with enforced rules.
FR#6 – Timely Response to Events: Detect abnormal or unauthorized commands, setpoints, or behaviors generated by AI.
These requirements ensure that AI enhances operations without becoming an uncontrolled control element.
- Policies and Procedures
Technology alone is not enough, so ISA/IEC 62443-2-1 emphasizes the importance of policies and procedures, including:
- AI governance and approval processes
- Change management for AI models and logic
- Incident response for AI-related cyber events
- Clear definition of roles and responsibilities
Without governance, even technically secure AI deployments can drift into unsafe operating conditions.
How CS4 Supports Secure AI Integration
CS4 by DTS Solution enables organizations to adopt AI in OT/ICS safely and systematically by:
- Embedding ISA/IEC 62443 principles into architecture and design
- Supporting zone & conduit modeling for AI use cases
- Enforcing access control, monitoring, and integrity protection
- Aligning AI deployment with OT lifecycle phases (design, operation, maintenance)
This ensures AI becomes a controlled, auditable, and resilient capability, not an unmanaged risk.
Conclusion
AI integration in OT/ICS is not just a technology challenge; it is a risk management and engineering challenge.
By applying ISA/IEC 62443 correctly:
- Innovation can coexist with safety
- Optimization can coexist with availability
- AI can be adopted without compromising control system integrity
The goal is not to block AI but to engineer trust in AI-enabled OT systems.